If you manage an IT environment in Australia, you already know that the Australian Cyber Security Centre’s (ACSC) Essential Eight framework is no longer just a “good idea”—it is rapidly becoming a mandatory baseline for doing business.
Mitigation Strategy #1 is Patch Applications. But the ACSC doesn’t just want you to patch; they dictate exactly when you patch.
If you are relying on manual updates or basic Microsoft WSUS, achieving the strict ACSC timeframes across hundreds of endpoints and third-party apps (like Adobe, Chrome, or Zoom) is practically impossible. Here is a brutally honest breakdown of the top 5 automated patch management tools built to keep Australian organizations compliant, secure, and insurable.
Understanding ACSC Compliance: The 48-Hour Rule
To rank at Maturity Level 1, 2, or 3 of the Essential Eight, you must satisfy strict deployment timeframes. The most critical rule that IT managers fail on is the 48-Hour Mandate.
Under the ACSC guidelines, if a vulnerability in an internet-facing service or commonly targeted application has a “working exploit” or is rated as “critical,” it must be patched within 48 hours of the vendor releasing the update. For non-critical, internal vulnerabilities, you generally have a two-week to one-month window depending on your targeted maturity level.
Furthermore, you must run automated vulnerability scanners (weekly or fortnightly depending on your level) to prove that the patches actually installed successfully.
The Business Angle: Why This is More Than Just an IT Problem
Patch management software is no longer an “IT expense”—it is a core business continuity asset.
- The Cyber Insurance Prerequisite: In 2026, Australian cyber insurance providers will deny coverage or refuse payout on a ransomware claim if you cannot prove you actively patch your systems. Patching software provides the audit trail insurers demand.
- Protecting Profit Margins: A single successful ransomware attack caused by an unpatched vulnerability can halt operations for weeks. The average cost of a cyber incident for an Australian SME is currently soaring past $56,000. Paying a few dollars a month per computer for automated patching is the cheapest insurance policy your business can buy.
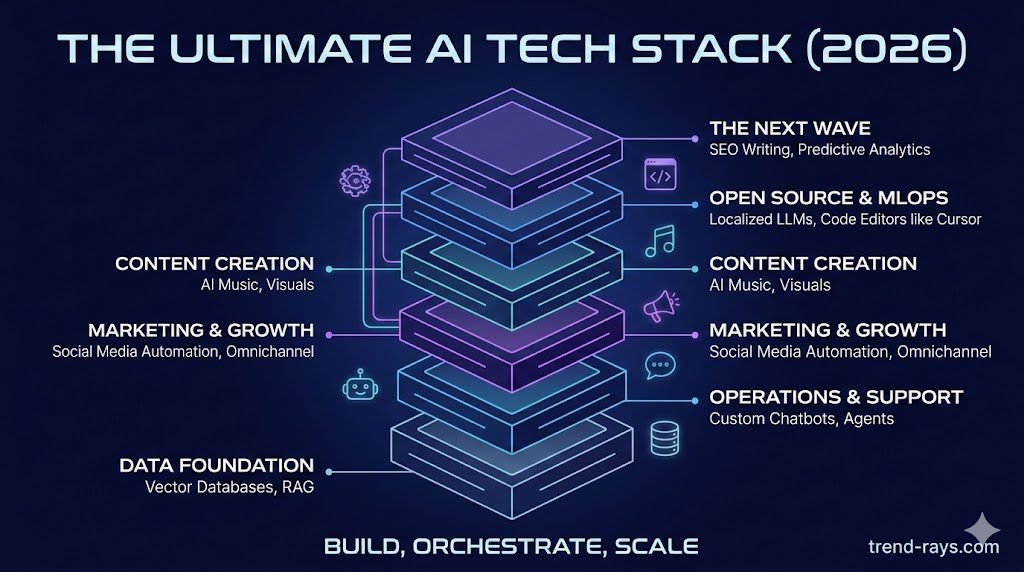
How Automation is Transforming the Industry
The patching industry has completely transformed. Five years ago, IT managers spent their weekends manually pushing updates, praying a server wouldn’t crash.
Today, the industry is driven by Cloud-Native Agents and Machine Learning. Modern tools don’t care if an employee is sitting in a corporate office in Sydney or a coffee shop in Bali; the cloud agent forces the patch over any internet connection. Furthermore, predictive ML algorithms now simulate the patch before deployment, warning IT teams if an update is likely to cause a “Blue Screen of Death” before it ruins the company’s network.
General Advantages & Cost Expectations
- The Advantages: Beyond pure compliance, automated tools eliminate “IT burnout.” They handle third-party applications (which Microsoft natively ignores), force automatic reboots outside of business hours, and provide one-click compliance reports for auditors.
- The Cost Expectation: Most modern patch management tools operate on a “per-endpoint” (per device) pricing model. For a high-quality automated tool, expect to pay anywhere from $2.50 to $6.00 AUD per device, per month.
At a Glance: Top 5 Patching Tools for ACSC Compliance
| Software | Best For… | Standout Feature | Deployment |
| ManageEngine Patch Manager Plus | Comprehensive OS & 3rd-Party patching | Supports 850+ third-party apps | Cloud & On-Premise |
| Automox | Remote and hybrid workforces | Cloud-native, incredibly fast execution | Cloud only |
| NinjaOne | MSPs and lean IT teams | Unified RMM and patching console | Cloud only |
| JetPatch | Enterprises needing predictive success | Machine-learning patch prediction | Cloud & On-Premise |
| Ivanti Security Controls | Complex, legacy enterprise environments | Deep vulnerability assessment sync | On-Premise heavily |
The Top 5 Patch Management Tools
1. ManageEngine Patch Manager Plus (Best All-Rounder)
When it comes to hitting Essential Eight compliance across a mixed-device environment, ManageEngine is one of the most robust platforms available. It natively supports automated patching for Windows, macOS, Linux, and over 850 third-party applications.
- How to Use It: You install the central server (or use their cloud version) and deploy a lightweight agent to all your endpoints. You then create an “Automated Patch Deployment” (APD) task. You set a rule stating: “If Adobe Reader releases a Critical Patch, test it automatically on the IT team’s computers on Day 1, and roll it out to the rest of the company on Day 2.”
- The ACSC Advantage: The APD feature ensures you easily hit the 48-hour mandate without human intervention.
- Estimated Cost: Highly affordable for SMEs. Starts around ~$2.00 to ~$3.50 AUD per endpoint/month depending on the edition.
2. Automox (Best for Remote and Hybrid Workforces)
If your workforce is fully remote and rarely connects to a corporate VPN, relying on a traditional on-premise patching server will cause you to fail an ACSC audit.
- How to Use It: Automox is purely cloud-native. You deploy the agent via a quick script or Group Policy. Once installed, you log into the web console and create an “Automox Policy.” You can link Automox directly to your vulnerability scanner. If the scanner detects a CVE, Automox automatically fetches the exact patch required and pushes it to the laptop, forcing a reboot at 2:00 AM local time.
- The ACSC Advantage: It operates with incredible speed and visibility, completely bypassing the need for complex internal network configurations.
- Estimated Cost: Premium cloud pricing. Starts around ~$4.50 to ~$6.00 AUD per endpoint/month.
3. NinjaOne (Best for Lean IT Teams and MSPs)
NinjaOne is highly popular among Australian Managed Service Providers (MSPs) and lean internal IT teams who need to manage patching alongside general IT support tickets.
- How to Use It: NinjaOne is a full RMM (Remote Monitoring and Management) tool. After installing the agent, you use the unified dashboard to configure “Patching Policies.” If an update fails, it automatically generates a support ticket in your helpdesk so a technician can remote into the machine with one click and fix the issue.
- The ACSC Advantage: It bridges the gap between identifying a missing patch and immediately opening a workflow to remediate it.
- Estimated Cost: Pay-per-device RMM pricing. Exact costs require a custom quote, but generally sit in the ~$4.00 AUD per endpoint range.
4. JetPatch (Best for Predictive Patch Success)
Patching breaks things. It is the number one reason IT teams delay rolling out updates, which subsequently causes them to miss their 48-hour compliance window.
- How to Use It: JetPatch uses machine learning for “predictive patching.” You integrate it with your vulnerability scanner (like Qualys or Tenable). JetPatch analyzes your specific environment and historical data to predict if a patch will succeed. If the dashboard shows a 99% predicted success rate, you confidently click ‘Execute’ for an automated ring deployment.
- The ACSC Advantage: It removes the fear of downtime, allowing IT managers to aggressively meet the 48-hour rule without breaking core infrastructure.
- Estimated Cost: Enterprise-grade pricing. Custom quotes only, typically reserved for massive organizations.
5. Ivanti Security Controls (Best for Complex Enterprises)
For massive Australian universities, government departments, or hospitals managing legacy servers and highly complex networks, Ivanti is a heavyweight contender.
- How to Use It: Ivanti bridges the gap between the security team and IT operations. You import a CVE list directly from your security team’s vulnerability scanner. Ivanti automatically maps those specific vulnerabilities to the exact vendor patches required. You then build a deployment template that pushes those patches exclusively during approved weekend “change freeze” windows.
- The ACSC Advantage: It provides the granular, audited proof that massive enterprises need to show government regulators they have mitigated specific, identified threats.
- Estimated Cost: Complex node-based enterprise licensing. Custom quotes only.
Frequently Asked Questions (FAQ)
Does Microsoft WSUS meet Essential Eight requirements?
On its own, Microsoft Windows Server Update Services (WSUS) struggles to meet Essential Eight compliance. While it patches Microsoft OS effectively, it lacks native, automated capabilities to patch third-party applications (like Chrome, Zoom, or Adobe Reader), which the ACSC explicitly requires.
What is the difference between Maturity Level 1 and Level 3 patching?
At Maturity Level 1, the focus is patching internet-facing servers and critical apps within 48 hours, with vulnerability scanning done fortnightly. At Maturity Level 3, the requirement tightens. You must scan for vulnerabilities at least weekly (or daily for internet-facing services) and patch all applications with exploits within 48 hours, while aggressively removing legacy software that is no longer vendor-supported.
Can I use a free tool for patch management?
While some open-source scripts exist, free tools lack the reporting dashboards, third-party application support, and automated vulnerability mapping required to pass an official Essential Eight audit or satisfy a cyber insurance underwriter.