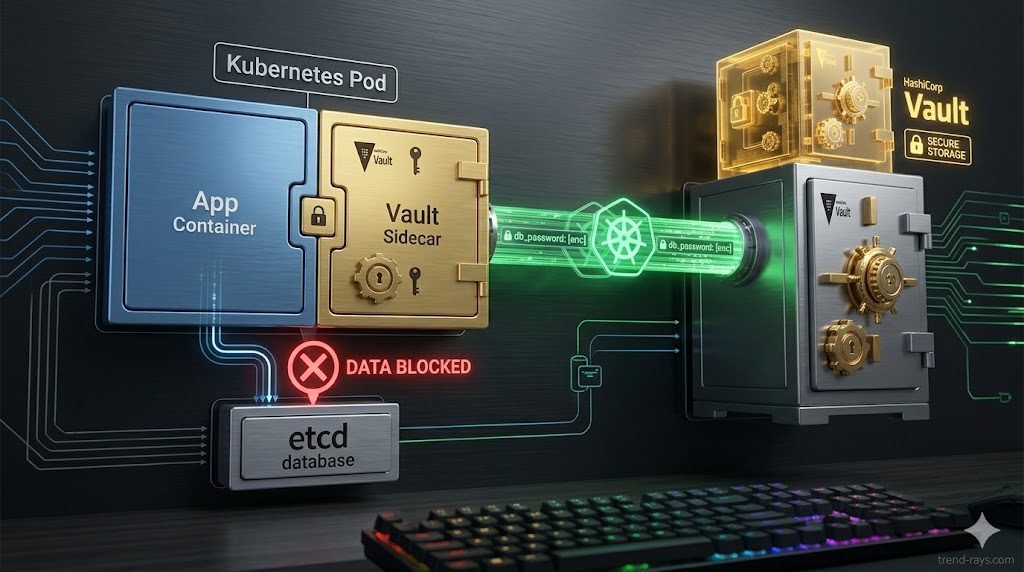
Native Kubernetes Secrets do not provide enterprise-grade security because they are merely Base64-encoded, not encrypted, meaning anyone with access to the cluster’s etcd datastore can read the enterprise’s database passwords and API keys in plain text. The Solution: To achieve secure Kubernetes secrets management, DevSecOps engineers must integrate HashiCorp Vault. By deploying the Vault Agent Injector via a Mutating Admission Webhook, pods can authenticate using their native Kubernetes Service Accounts (via JWT) and dynamically retrieve temporary, auto-rotating secrets directly into their in-memory file systems, entirely bypassing native Kubernetes storage.

The DevSecOps Crisis: Why Native Kubernetes Secrets Are a Trap
As enterprises scale their microservices architectures, managing the passwords, API tokens, and TLS certificates (collectively known as “secrets”) becomes a logistical nightmare.
The default instinct for many junior developers is to use the native Secret object provided by Kubernetes. This is a massive security trap. By default, native Kubernetes Secrets are not encrypted; they are simply Base64-encoded. Base64 is a data-formatting scheme, not a cryptographic cipher. Anyone who can run a basic kubectl get secret command, or any threat actor who compromises the cluster’s underlying etcd database, can instantly decode your production database credentials in milliseconds.
While you can enable etcd encryption at rest, this still leaves a massive vulnerability: the secret is exposed to the Kubernetes control plane, and the lifecycle of that secret (when it expires and how it is rotated) must still be managed manually by humans. In a 2026 threat landscape, human-managed passwords are the primary vector for data breaches.
The CFO’s Nightmare: The $100,000 GitHub Commit
For the CFO, DevOps security is not just an IT metric; it is a massive financial liability.
When developers find secrets management too difficult, they engage in shadow workarounds—often hardcoding AWS IAM access keys directly into their application’s source code. If that code is accidentally pushed to a public GitHub repository, automated scraping bots will find the keys within seconds.
Within minutes, hackers will use those exposed API keys to spin up hundreds of massive, GPU-optimized cloud servers to mine cryptocurrency. By the time the DevOps team wakes up, the company has incurred a $100,000 AWS compute bill (a catastrophic failure we previously addressed in our ).
Deploying an enterprise-grade secrets manager like HashiCorp Vault acts as an insurance policy, separating the secret from the source code and protecting the company’s operating margins from accidental developer negligence.
Productivity & Developer Toil: Reclaiming Engineering Hours
The most overlooked advantage of Vault is the productivity angle. In a legacy environment, if a database password changes, a developer must manually update the Kubernetes secret and trigger a rolling restart of the pods. This “toil” adds up across hundreds of microservices.
By using dynamic secrets, Vault creates the credentials on the fly. The developer never sees the password, never manages the YAML, and never has to wait for a security ticket to be cleared. This architectural shift moves the security team from being a “blocker” to an “enabler,” allowing engineers to spend their hours building revenue-generating features rather than managing infrastructure rot.
The ROI of Automated Secrets Management
From a financial perspective, the risk of a secrets leak is a “Tail Risk” event—low probability, but catastrophic impact. Furthermore, for companies pursuing SOC-2 or HIPAA certification, manual secrets management is an audit nightmare. Each manual rotation must be logged and verified. HashiCorp Vault provides an automated audit trail, effectively lowering the cost of compliance by 40% through automated evidence collection and drastically reducing the liability of a breach.
Advanced Kubernetes Secrets Management Architecture (Deep Dive)
Architectural Comparison: Secrets Store CSI Driver vs. Sidecar Injector
Enterprise architects often debate between using the Sidecar Injector or the Secrets Store CSI (Container Storage Interface) Driver. To help architects decide on a deployment strategy, here are the advantages and disadvantages of both:
| Feature | Vault Agent Injector (Sidecar) | Secrets Store CSI Driver |
|---|---|---|
| Pros (Advantages) | Highly flexible; works with any app without code changes. Supports complex templating. | Uses fewer resources (no sidecar container). Native Kubernetes feel. |
| Cons (Disadvantages) | Increases memory footprint (extra container per pod). Pod must be restarted to update sidecar. | More complex setup; relies on the kubelet for secret mounting. |
| Best For | Legacy apps requiring specific config file formats. | High-scale clusters where resource overhead is a concern. |
For 2026 enterprise architectures, the Vault CSI Provider is increasingly preferred for massive clusters because it seamlessly syncs Vault secrets back into native Kubernetes Secrets specifically for legacy ingress controllers that still require them.
Kubernetes Service Account Authentication (JWT)
The first challenge is authentication: How does the Vault know that the pod requesting the database password is actually your legitimate payment application and not a malicious pod spun up by a hacker?
- The Architecture: Instead of giving the pod a static token, the integration utilizes the native Kubernetes Service Account (KSA). When the pod spins up, Kubernetes issues it a short-lived JSON Web Token (JWT). The pod presents this JWT to Vault. Vault then cryptographically verifies the signature of the JWT with the Kubernetes API server. If it matches, Vault grants access based on strict, role-based access control (RBAC) policies.
Deploying the Vault Agent Injector (The Sidecar Pattern)
You should never force your developers to rewrite their application code to manually fetch secrets via APIs. Instead, deploy the Vault Agent Injector.
- The Architecture: The Injector is a Kubernetes Mutating Admission Webhook. When a developer deploys a pod with specific annotations (e.g.,
vault.hashicorp.com/agent-inject: "true"), the webhook intercepts the deployment and automatically injects a secondary “Sidecar” container into the pod. This sidecar handles all the complex authentication with Vault, retrieves the secret, and writes it to a shared, in-memory volume (/vault/secrets). The primary application simply reads the password from that local file, completely unaware that Vault even exists.
The Secrets Store CSI Driver vs. Sidecar Injector
Enterprise architects often debate between using the Sidecar Injector or the Secrets Store CSI (Container Storage Interface) Driver.
- While the Sidecar Injector modifies the pod to fetch the secret, the CSI provider mounts secrets directly as file volumes via the
kubeletprocess. For 2026 enterprise architectures, the Vault CSI Provider is increasingly preferred for massive clusters because it uses fewer compute resources (no sidecar container required per pod) and seamlessly syncs Vault secrets back into native Kubernetes Secrets specifically for legacy ingress controllers that require them.
Dynamic Secrets and Auto-Rotation
The ultimate goal of DevSecOps is eliminating static credentials. With Vault, you can configure dynamic secrets rotation. Instead of storing a static PostgreSQL password, Vault dynamically generates a unique, temporary database username and password valid for only one hour. When the pod terminates, the credential is automatically revoked at the database level. Even if a hacker successfully steals the credential from the pod’s memory, it will be mathematically useless to them by the time they try to use it.
The Expert Troubleshooting Fix: Vault Injector Not Mutating Pods
The most common and frustrating issue DevSecOps engineers face during deployment is applying the Vault annotations to a deployment, only to find that the sidecar container fails to inject, leaving the application crashing with an Auth Error.
If your Vault Agent Injector is not mutating pods, the issue is almost always a Namespace Labeling Conflict or a Webhook Timeout.
The Fix:
- Check Namespace Labels: The Mutating Admission Webhook is often configured to ignore certain namespaces (like
kube-system) to prevent cluster death. Ensure your target application namespace does not have the labelname: vaultor any label that the webhook is instructed to bypass in itsnamespaceSelectorconfiguration. - Verify Network Policies: If your cluster uses Calico or strict NetworkPolicies, the Kubernetes API server (control plane) must be able to reach the Vault Injector service on port
443over the pod network. If the API server is blocked from reaching the webhook, the injection will silently fail. Run akubectl describe replicaset <app-name>to check for webhook timeout errors. - Validate Annotations: Ensure you are using the correct role annotation. The pod must have
vault.hashicorp.com/role: "your-vault-role"explicitly defined, or the sidecar will not know which RBAC policy to request from the Vault server.
Frequently Asked Questions (Kubernetes Secrets)
Why is Base64 encoding not secure for Kubernetes secrets?
Base64 is an encoding scheme designed to format data for safe transmission across networks, not to hide it. It requires no key or password to reverse. Anyone who can view the YAML file or query the Kubernetes API can instantly decode a Base64 string back into plain text using native terminal commands like echo "cGFzc3dvcmQ=" | base64 --decode.
What is the difference between HashiCorp Vault and AWS Secrets Manager for EKS?
AWS Secrets Manager is a fully managed cloud service tightly integrated with AWS IAM, making it ideal if your entire infrastructure is exclusively in AWS. HashiCorp Vault is cloud-agnostic. Enterprises use Vault when they have multi-cloud environments (e.g., spanning AWS, Azure, and on-premise servers) and need a single, unified secrets identity plane that works identically across all platforms.
Can HashiCorp Vault automatically restart my pod when a secret is rotated?
Yes, but it requires configuration. If you are using the Vault Agent Injector, you can use the vault.hashicorp.com/agent-inject-command annotation to run a script that triggers an application reload (like sending a SIGHUP signal) whenever Vault fetches a newly rotated secret, ensuring the app never experiences downtime due to expired credentials.

